Building an AI-Native Cyber Defense Strategy: A Practical Guide
Overview
In recent announcements, frontier AI labs like OpenAI and Anthropic have unveiled models that push the boundaries of reasoning, automation, and scale. These advances are not just academic—they are reshaping the cybersecurity landscape. For years, SentinelOne has championed the idea that the future of defense must be AI-native. This tutorial explores how organizations can leverage frontier AI to build a proactive, autonomous security posture. You'll learn the core principles, walk through implementation steps, and see real-world examples of how these concepts stop zero-day exploits and supply chain attacks.
Prerequisites
Before diving into this guide, you should have:
- A basic understanding of cybersecurity concepts (threats, vulnerabilities, attack surfaces)
- Familiarity with artificial intelligence and machine learning fundamentals
- Experience with security operations (SOC) workflows or tooling (helpful but not required)
- Access to a modern security platform that supports behavioral AI and automation (for hands-on exercises)
Step-by-Step Guide to AI-Native Cyber Defense
Step 1: Recognize the Shift from Vulnerability Metrics to Operational Risk
Traditional security focuses on finding and patching as many vulnerabilities as possible. However, frontier AI models, such as those from Google DeepMind and OpenAI, have shown that raw vulnerability counts often don't correlate with real-world risk. Many discovered bugs are not exploitable in production environments due to existing controls. The first step in an AI-native approach is to prioritize what actually matters: understanding your specific environment's configurations, runtime protections, and attack paths. Use AI to analyze telemetry and contextualize vulnerabilities by exploitability and impact.
Step 2: Implement Behavioral AI for Real-Time Detection
Frontier AI excels at reasoning about complex patterns. For cyber defense, this means moving beyond signature-based detection. Deploy behavioral AI models that learn normal baselines for endpoints, cloud workloads, identities, and networks. These models continuously monitor for anomalies—like unusual process execution, lateral movement, or data exfiltration. The AI should operate at machine speed, analyzing events in milliseconds. Example integration: Use an AI-powered agent that correlates file system changes, network connections, and user behavior to detect a zero-day exploit before any patch exists.
# Pseudocode for a behavioral anomaly detector
class BehaviorModel:
def __init__(self):
self.baseline = load_baseline_from_telemetry()
def analyze_event(self, event):
deviation = self.baseline.compare(event)
if deviation > threshold:
trigger_autonomous_response(event)
Step 3: Automate Response at Machine Speed
When anomaly detection identifies a potential threat, the response must be immediate. Manual intervention is too slow for zero-day exploits that can spread in seconds. Implement autonomous response capabilities that can isolate endpoints, block suspicious processes, or terminate compromised cloud instances without human input. The decision logic should be guided by AI that considers context—does the behavior match known attack patterns? Is the risk high? For example, during the recent LiteLLM supply chain attack, autonomous response at machine speed was the only effective antidote because the vulnerability was unpatched and traditional tools failed.
Step 4: Integrate Threat Intelligence with Internal Telemetry
Frontier AI models from labs like Anthropic and OpenAI can process vast amounts of threat intelligence. However, generic intelligence alone isn't enough. Combine external indicators with your own telemetry to tailor defenses. Use AI to correlate threat reports with your asset inventory, network diagrams, and risk scores. This enables you to proactively block known attack vectors and prepare for emerging ones. For instance, if a new vulnerability is disclosed in a widely used library, AI can scan your environment for instances of that library and apply virtual patches or enhanced monitoring.
Step 5: Apply AI-Native Principles to Supply Chain Security
Supply chain attacks exploit trusted relationships. Recent incidents involving Axios and CPU-Z highlight how malicious code can be injected into legitimate software updates. AI-native defense extends beyond your perimeter: it monitors the behavior of third-party integrations, code repositories, and CI/CD pipelines. Use AI to detect anomalous changes in build artifacts, unexpected network calls from trusted processes, or unusual privilege escalation within containerized environments. Autonomous response can then quarantine affected systems and roll back updates automatically.
Common Mistakes
When adopting AI-native cyber defense, avoid these pitfalls:
- Overreliance on vulnerability scanning: Patching every CVE wastes resources and neglects operational context. AI should prioritize exploitability.
- Ignoring the human element: Despite automation, security teams must train the AI models and review false positives. Involving analysts in model tuning is critical.
- Using siloed AI tools: Integrate detection, response, and threat intelligence into a single platform to avoid blind spots and delayed actions.
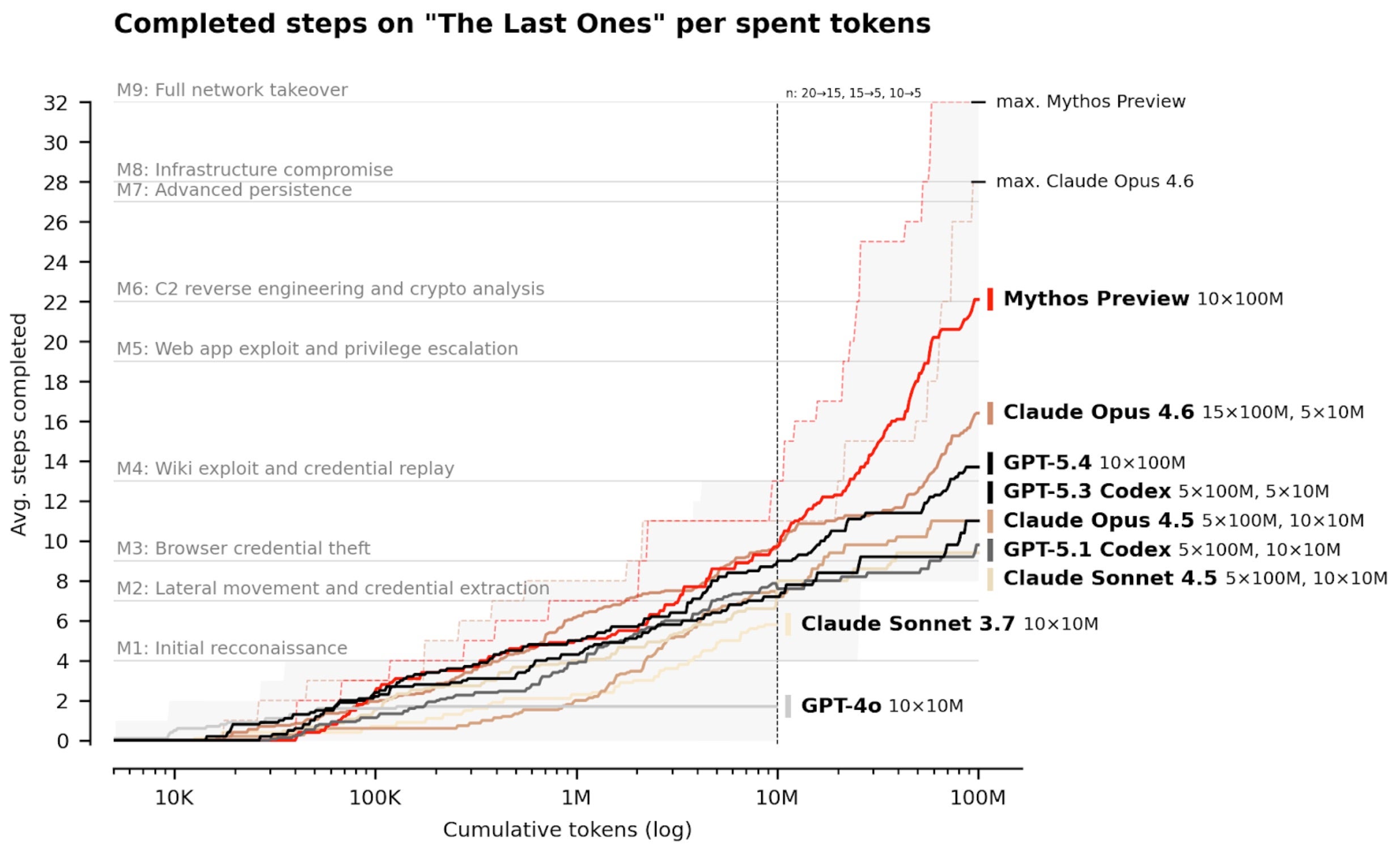
- Neglecting adversarial AI: Attackers also use frontier AI. Your defense must be adaptive and capable of countering AI-generated attacks.
Summary
The convergence of frontier AI and cybersecurity is accelerating a shift from reactive, signature-based defenses to proactive, autonomous protection. By focusing on operational risk, deploying behavioral AI, automating response, integrating threat intelligence, and securing supply chains, organizations can stay ahead of modern threats. SentinelOne's long-standing partnerships with frontier labs demonstrate that the future of defense is AI-native—built to operate at machine speed and stop zero-day exploits that no other solution can. Embrace this approach to future-proof your security operations.
Related Articles
- The Quiet Revolution: How AI-Driven Vulnerability Discovery Reshapes Cybersecurity
- 8 Critical Facts About the MetInfo CMS RCE Vulnerability (CVE-2026-29014)
- How to Stay Ahead of Cybersecurity Mergers and Acquisitions: A Practical Guide
- Supply Chain Attack Hits 1,800 Systems via Compromised Packages
- The Amazon SES Threat: How Cybercriminals Exploit Trusted Infrastructure for Phishing Attacks
- 7 Things You Need to Know About the Stealthy Credential Theft in Open Source Package element-data
- Lessons from the Snowden Leaks: A CISO's Guide to Insider Threat Detection and Organizational Culture
- How to Respond to a Critical Git Push RCE Vulnerability: A Step-by-Step Incident Response Guide